🔐 Email Server Security is Important #
Why would you need to improve your email server security? Firstly, you have taken the time to set up secure, industry leading technology like OpenSMTPD, Dovecot and Rspamd and followed best practices. On top, you run your server on a secure operating system like OpenBSD and have chosen a secure cloud provider, so what else could you have to do? Basically, on top of having an intrinsically secure server, you want to ensure your reputation is protected beyond the walls of your organization. Typically, you can do this by setting a few DNS records. It is so important to set these records. First, it gives you credit with large players, like Google and Microsoft so that the carefully crafted emails your marketers created are not sent straight to spam folders and ignored. Secondly, you protect your brand, making it harder for spammers to impersonate you.
Sounds interesting? Then let’s carry on to the seven tips for improving email server security.
📧 7 Tips to Improve Email Server Security #
1. BIMI #
- What is it? Brand Indicator Message Identification shows your brand logo in the email recipient's inbox when the email is deemed to be legitimate.
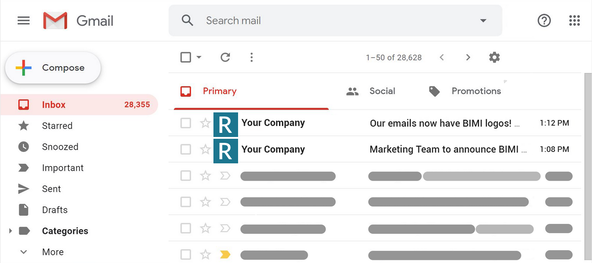
- How does it improve security? Basically, seeing your brand logo is a quick and easy way for the recipient to recognize a legitimate message, requiring zero technical knowledge. BIMI relies on a DMARC check to verify the mail was sent from your domain.
- How do you set it up? First, set up DMARC (see DMARC instructions below). With that done, serve an SVG logo from your website. The SVG logo needs to be in SVG Portable/Secure format . Finally, add the following DNS record, linking to the SVG image you set up.
default._bimi.example.com TXT “v=BIMI1; l=https://example.com/logo.svg;a=;”
If all went well, recipients will now see your logo in their inbox whenever they receive a message from you.
- How do you test it? Go to bimigroup.org/bimi-generator/ .
2. SPF #
- What is it? Sender Policy Framework indicates which hosts are authorized to send email for your domain.
- How does it improve security? SPF authenticates emails sent from your email addresses, checking emails are sent from an authorized domain. SPF is used by mail exchanges. An exchange can then mark unauthenticated email as spam.
- How do you set it up? create a TXT DNS record, which includes the IP address of your main mail server. If you want to send email via external domains (as well as your own) you need to include these too, in the same record. For example, you might include services used to send your automated emails, like SendGrid here.
- How do you test it? Go to dmarcanalyzer.com/spf/checker/ .
example.com. IN TXT v=spf1 a mx ip4:123.234.123.234 include:sendgrid.net ~all
3. DKIM #
- What is it? DomainKeys Identified Mail relies on cryptographic keys included in sent emails. Exchanges process the key, thus determining if the email origin is genuine. Beyond that, it can check the content of the message has not been altered since it was sent from your server.
- How does it improve security? When you send a message, it is signed with your private cryptographic key, which you keep secret. Third parties (such as exchanges) can analyse the message, making use of your public key and verify the email as genuine. Without your private key, it is difficult for someone to forge a message from your server.
- How do you set it up? You need to generate a pair of cryptographic keys. Due to limitations on the maximum length of TXT record with some service providers, use a 1024-bit key (for other applications, you would typically use a 4096-bit key). Once you have a 1024-bit key working, try 2048 bits. The private key needs to be integrated into your mail server. If you are using Rspamd spam filtering on your email server, then it is as simple as just including the path to the private key in the configuration file.
- How do you test it? Use the free tool at DKIMValidator.com . It will ask you to email them from your server. It then runs an analysis which includes giving you a SpamAssassin score as well as verifying your DKIM setup.
Next up use the entire public key to generate a TXT DNS record:
default._domainkey.example.com. IN TXT "v=DKIM1;k=rsa;p=<YOUR_PUBLIC_KEY>;h=sha256;t=s;h=sha256
here t=s blocks emails being sent from subdomains.
Remove this if not needed.
4. DMARC #
- What is it? Domain-based Message Authentication, Reporting, and Conformance is a standard which can be used on your server to define what should happen if a message fails authentication. Here the choices are quarantine, reject or allow. Reports can be sent to your server admin about all messages which fail.
- How does it improve security? Setting up reject can be used to stop spoofed spam messages getting to recipients and harming your brand. On top, DMARC is used together with BIMI, mentioned earlier.
- How do you set it up? This just needs a TXT DNS record. Here
ruais the recipient address for reporting andpctdetermines what percentage of your emails should be filtered.
_dmarc.example.com. IN TXT "v=DMARC1; p=reject; pct=100;rua=mailto:[email protected]"
- How do you test it? Go to mxtoolbox.com/dmarc.aspx .
5. TLS RPT #
- What is it? TLS reporting is a way for exchanges to report errors.
- How does it improve security? By monitoring issues, TLS RPT helps you maintain a secure mail server.
- How do you set it up? Just set a TXT DNS record which includes a reporting email address:
_smtp._tls.example.com. TXT "v=TLSRPTv1; rua=mailto:[email protected]"
- How do you test it? Go to mailhardener.com/tools/tls-rpt-validator .
6. MTA STS #
- What is it? MTA Strict Transport Security tells other servers only to use encrypted connections to your server. If you are familiar with web server security, it is analogous to HSTS.
- How does it improve security? Other servers will send mail encrypted, so third parties will struggle to tamper with them.
- How do you set it up? Setup is a little more involved here. As
well as a DNS record, you need to set up a secure web server. This will serve
a file at
https://mta-sts.example.com/.well-known/mta-sts.txt. The contents of the file will be your mail server's MTA STS policy. This file is a little fiddly, to set up. It must have windows-style CRLF line endings.
Start with a test version:
version: STSv1mode: testingmx: mail.example.commax_age: 604800
Here the max age, specified in seconds, is one week. Once you are happy it is working, implement the production version (bumping maximum age up to 120 days):
version: STSv1mode: enforcemx: mail.example.commax_age: 10368000
Set up a free TLS certificate with Let's Encrypt for the web server. Finally, add these MX records:
mta-sts.example.com. A 123.234.123.234mta-sts.example.com. CAA 128 issue "letsencrypt.org"
The first is the main MTA STS record, while the second tells servers only to accept certificates signed by Let's Encrypt for connection to the web server.
- How do you test it? Go to esmtp.email/tools/mta-sts . You can also test using the MTA-STS validator .
7. Client Certificates #
- What is it? Normally, to send email from your server, the sender needs a password. Here you add the need for a certificate as well as a password.
- How does it improve security? Helps protect against users who set weak passwords or do not manage passwords securely.
- How do you set it up? This is not too much work if you are using OpenSMTPD. You just need to create a private server certificate, a certificate authority and then generate clients certificates for end users. Using OpenSMTPD, import the certificate into the config and then require it for sending email:
ca "mailca" cert "/etc/mail/ca.crt"listen on egress port 587 tls-require pki mail.example.com ca "mailca" auth <credentials> filter "rspamd"
Also, see the OpenBSD man page for smtpd.conf for more details. Of course, tell me if you would like more details on setting this up, I could write a post on the full SMPTD setup.
Note that not all mail clients support client certificates. Thunderbird, by Mozilla, is a client which does support them, though.
💯 Improve Email Server Security — Take it to the Next Level #
On account of the 7 tips, you should already have quite a secure server. Even so, if you wanted to go the extra mile, you might consider setting up DNSSEC. This is a framework for clients verifying that the IP address returned from their DNS server, for your mail server, is correct. It involves some work to set up. In contrast to the other tips listed here, it also involves continued time investment for maintenance in keeping DS records up-to-date.
Let me know if you eventually opt for DNSSEC. Keen to hear how the experience was.
🙏🏽 Improve Email Server Security: Feedback #
I hope you have you found this post useful on the whole. Though the post is already quite long, let me know if there is anything still missing. What steps do you take to improve email server security besides these? I'm undeniably keen to hear. Also, get in touch if you want to see other posts in this area. If you have found this post useful and can afford even a small contribution, please consider supporting me through Buy me a Coffee.
Finally, feel free to share the post on your social media accounts for all your followers who might find it useful. You can get in touch via @askRodney on Twitter and also askRodney on Telegram . Alternatively, see further ways to get in touch with Rodney Lab. We post regularly on accessible Gatsby website development as well as OpenBSD-centric content. Also, subscribe to the newsletter to keep up-to-date with our latest projects.

